Outrunning the Frontrunners
How Shimmer Minimizes the Market Manipulation Practice of MEV in DeFI
TL;DR:
MEV is the decentralized finance (DeFi) equivalent of market manipulation but on a scale not achievable in traditional finance. Its roots lie in the nature of the blockchain consensus: the ability for miners/validators/bots to insert their own transactions into the block and order the transactions within the block for their benefit. Shimmer holds the key to minimizing MEV by running consensus not on the finalized block but on the batch of transactions, thereby eliminating the auction ordering mechanism.
As the world of decentralized finance (DeFi) grows, so do opportunities for those seeking to take advantage of the system through various controversial strategies. One such strategy is known as MEV, which stands for ‘Miner Extractable Value’ or, increasingly, ‘Maximal Extractable Value’. In MEV, bots crawl through mempools (the places where buy/sell transactions are kept in waiting before being processed and where all details of a transaction can be seen by anyone) looking for the juiciest transactions to essentially hijack it during the mining process for personal gain. For example, when a transaction is placed on a DEX to buy a large amount of a certain token, or a high slippage transaction is placed into the mempool, a bot can place a buy order just before and a sell order right after the transaction (sandwich attack). This increases the price of the token buy for the victim and returns immediate profit for the bot, earning such profit in the same block with zero risk. Every day millions are taken from right under the noses of users in this manner often without being noticed, or until it's too late. This attack is possible because miners/validators order transactions via an auction system with the highest gas fees being processed first, the attacker can place their transactions in an order to maximize their returns.
The memepool provides attackers with privileged knowledge about imminent transactions which only bots can take advantage of due to the high-speed processing required. Essentially, this is some form of market manipulation, which is considered illegal and unethical behavior in traditional stock markets but is very common in crypto markets. Some believe the integrity of crypto may be at stake by this and minimizing MEV would revolutionize DeFi – and that is precisely what the Shimmer network delivers.
Why MEV is bad for DeFi
Concerns over MEV were first raised as soon as 2018, and have been growing ever since. In the developer community around Ethereum, where MEV is especially prevalent, it is hotly debated but not always considered a negative phenomenon.
One of the main reasons that MEV is controversial is because critics accuse it of pushing up transaction costs: “It’s more expensive than ever to use the Ethereum blockchain” is the headline in this article on CoinDesk.com about the effects of MEV. It is also accused of causing chain instability (“MEV inherently encourages consensus instability”), and eating up processing power across the entire network. And as always, it is the retail or individual traders trading with their personal money that is hit the hardest by MEV abuse.
Despite, or because of this, MEV is huge: the total extracted MEV since the beginning of 2020 is officially north of $750 million, according to research by Flashbots (an organization that tracks the spread of MEV), but arguably maybe even more.
Causes of MEV
The root cause of MEV reaches back to the very nature of the permissionless consensus protocols used by blockchains: the Nakamoto Proof of Work (PoW) consensus. In the PoW consensus, each miner determines the content of the block to its liking and thus computes its own version of how the blockchain should proceed. Then, all miners in the network run a PoW race to see whose block will be included in the chain. The block mined by the lucky winner will likely be included in the blockchain. The block will of course contain transactions favorable to its miner, most notably the newly-minted tokens sent to the miner’s account.
This consensus system presents a huge temptation for the miner to manipulate the block’s content for its own benefit.
This behavior is not limited to miners alone. Many blockchains use the gas price to define the ordering of a transaction. The more gas you pay the sooner your transaction will execute within a block (it’s a predictable ordering). By looking at the gas cost for transactions in the mempool one can easily place another transaction right before or after without any connection to the miners at all.
Types of MEV attacks
A popular method of extracting MEV by arbitrageurs is running bots that engage in front running, back running or sandwich trading.
In the world of trading, “Frontrunning” refers to a predatorial transaction that exploits inside knowledge about a big transaction before it hits the market. In DeFi/crypto terms, this involves bots crawling mempools and copying a transaction with an increased gas price, thereby moving it forward in the chain of priority ahead of the copied transaction. Taking it further, the bots enter their sell order at a lower price than the original transaction: when all these transactions are executed, this is known as sandwich trading.
When an MEV strategy targets liquidity loans issued after price oracle updates, it is known as liquidation. Yet another type of MEV is known as Time Bandit attacks, which reward miners for the reorganization of past blocks. If the reward is high enough, miners could be incentivized to put forward competing blocks containing adjusted transactions at the expense of users and other network stakeholders.
This is not an exhaustive list of MEV attacks but should show that the opportunities for nefarious abuse of MEV are considerable in the field of decentralized exchanges. Some argue that MEV plays a helpful role by incentivizing miners to validate the network; however, this is a controversial point of view. The general sentiment is that preventing MEV is beneficial for the future of decentralized finance. However, it is not easy given the very nature of the permissionless PoW consensus. Therefore, MEV remains a serious and largely unsolved problem for blockchains.
There are measures that traders can take to minimize the damage: for example, it is possible to set a limit on the amount of slippage you are willing to contemplate in your buy/sell transaction, meaning that if the transaction price shifts beyond that limit, the order is automatically canceled. And there are design elements that dApp designers can include in their smart contracts to hide transactions from attackers. However, these measures are hardly a defense against the range of tempting incentives for miners to take advantage of MEV (as rational economic actors can be expected to).
These incentives pose a very real threat to DEXs and decentralized finance in general: “The future is only going to get scarier”, predicts Dan Robinson and Georgios Konstantopoulos in their essential reference on MEV, “Ethereum is a Dark Forest”.
A revolution in DeFi
Enter Shimmer. Because it is not possible to order transactions in the blocks of smart contract chains on Shimmer, possibilities to run MEV strategies on Shimmer are minimzed.
The IOTA Smart Contracts framework for Shimmer holds a solution to the MEV problem. In IOTA Smart Contracts, prevention of MEV lies in the way consensus on the state is run in the smart contract chain.
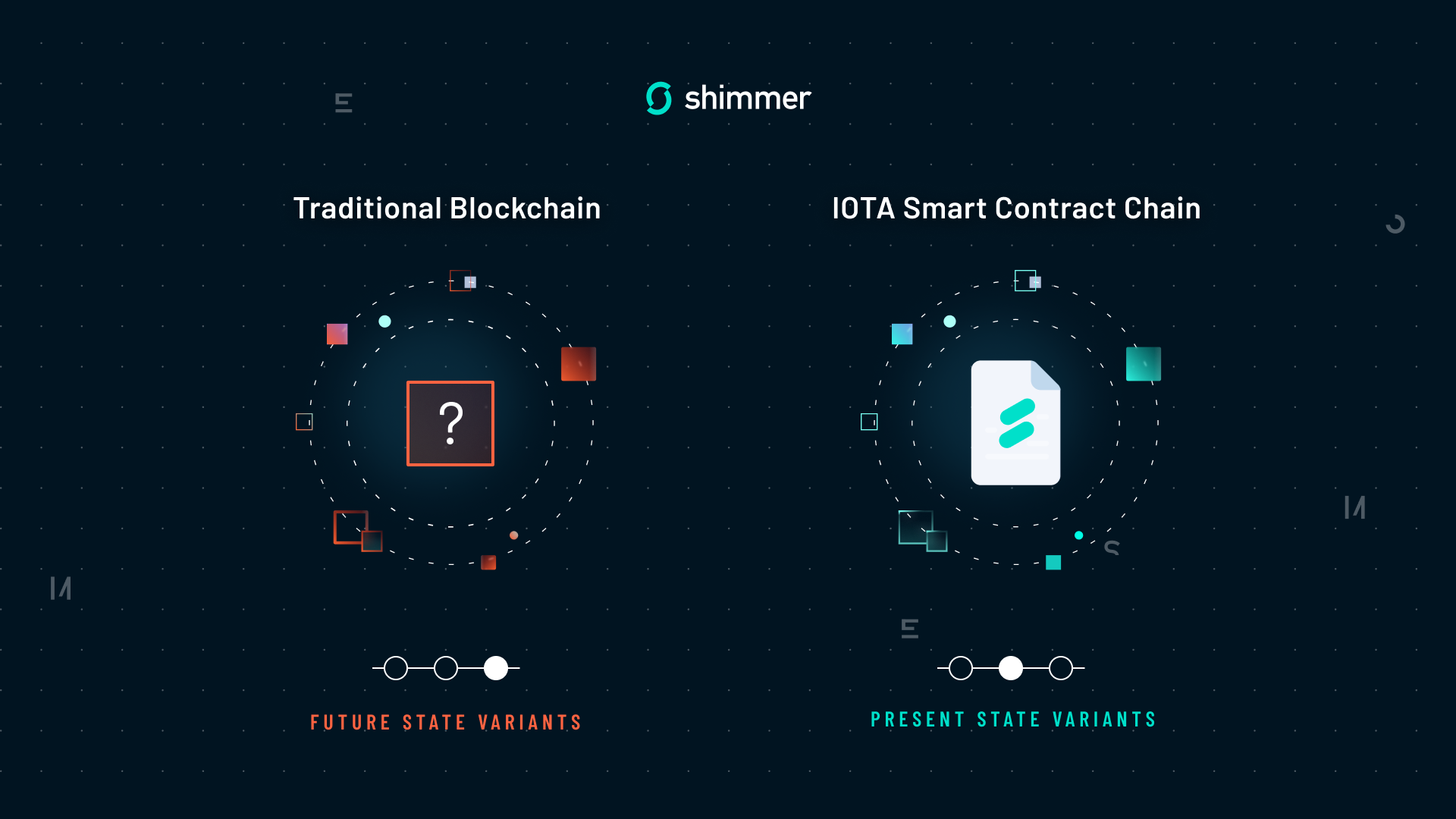
A smart contract chain runs consensus on the batch of requests (incoming transactions) before running the requests on the virtual machine and computing the block. This is different from the usual blockchain consensus paradigm, where miners first each compute a block before the network decides which block will be next in the chain.
In other words, the IOTA smart contract chain reaches consensus on which version of the present state to use for the state transition, while traditional blockchain runs consensus by choosing among many variants of the future state.
Therefore, in IOTA Smart Contracts, the validator node cannot by itself determine the content of the block: each request in the block is a consensus of the entire committee of validators.
And that’s not all: the order of the batch is randomized in a deterministic pseudo-random way that is unpredictable to the validators. The HoneyBadger Asynchronous Common Set (ACS) consensus used in IOTA Smart Contracts generates randomness by using properties of the threshold signatures. This makes aggregated signatures unpredictable for less than 67% of colluding validators, which is a highly unlikely situation. The generated randomness is used to order the batch of requests.
This way, IOTA Smart Contracts make it practically impossible to influence the content of the block and the order of transactions in it. Even if requests are proposed by validator nodes based on a self-serving criterion, (for example a fee), the final order of requests in the block remains unpredictable. This unpredictability dramatically minimizes the chances for the validator node to use insider information from the mempool to post its own requests to extract MEV.
So, thanks to the consensus mechanism used in IOTA Smart Contracts and randomized batch ordering, Shimmer not only offers security and reliability to anyone using it to trade crypto on decentralized exchanges but offers a light in the ‘dark forest’ of DeFi.



